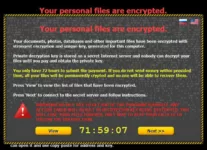
Ransomware should be scaring us more than it is. It is becoming increasingly invasive, increasingly common, and they aren’t just attacking individuals and small businesses anymore they are attacking hospitals and law enforcement agencies (who apparently don’t follow their own “don’t pay blackmail advice”). It won’t be long until we can measure these attacks in lives lost. One successful attack at a critical time during the normal operation of a hospital could deny patents timely medication or force mistakes that could easily cost lives. There, of course, is the common advice not to pay these financial terrorists (and likely not long before they are classified as such) but this is typically from folks that aren’t faced the choice of paying or being out of business.
What I think is interesting is this mirrors the early days of protection rackets where organized crime would demand payment in exchange for not destroying your business or doing you harm. These folks eventually evolved to actually provide protection from other gangs working the same business model and in some areas paying protection is still good business as a result. It is doubtful that will ever be true with this class of attack.
There are a lot of us writing about how to deal with this but the key advice is to have processes and protection to both prevent the installation of Ransomware and to rapidly identify an attack in process and mitigate it.
We used to think Apple computers were relatively safe because there were so few of them but numbers have increased and because Apple shops typically lack aggressive defenses and often exist in mission critical production areas for some industries, and there demographic is relatively wealthy older people (who are more likely to pay ransom) that is no longer the case. In fact Apple machines because they have been largely left alone up till now suddenly may be the most vulnerable because the users aren’t as well trained in defense and the security industry has largely ignored Apple.
Defense In Depth
Part of a good defense in depth is to have tools standing by to undo the damage done. Kaspersky increasingly becoming the most active of the traditional anti-virus firms providing that service. They just recently defended against a CryptXXX attack this month where the folks using the tool were demanding $500 per machine infected to return that machine to service. Apparently this nasty bit of code also scans the machines it encrypts for Bitcoins and then automatically transfers those coins to the attacker. What is fascinating about this tool is that the infection comes from infected websites but the attack tool delays execution so they aren’t able to easily tell which website is infected.
This kind of thing could quickly have companies going back to aggressively only allowing employees to go to sites that are assured safe and blocking the rest of the internet. Simply browsing the web looking for stuff has never been more dangerous.
Aggressive Defense
Another increasingly popular tool is from Varonis which aggressively limits unauthorized access and immediately alerts when unusual behavior is noted surrounding your data. It is one of the most aggressive monitoring/fast defense tools in market and it is one of the most effective tools in not only identifying a Ransomware attack but in catching data theft in progress. They regularly update data threat models and aggressively monitor user behavior to identify user identity theft or any malware that attempts to take the identity of a user to do damage or steal data.
This class of behavioral based security software is particularly handy against a threat landscape that is rapidly changing because it focuses on the constants not the actual technologies used to do the damage or steal the data. Those constants are unauthorized access, and unusual or suspicious activity. Generally both ransomware and data theft are tied to an unexpected or unauthorized event but if you can trigger an alert if either happen you have a defense against attacks even before the folks that make them figure out what they are going to do.
Wrapping Up:
Given the payload delivery for this class of malware continues to evolve moving from tricking users to install it to being placed in trusted websites so it self-executes with a delay so you can’t easily figure out where it came from our need to protect against it is only increasing. Having to recreate years’ worth of accounting data, recover a key development product, or even get back your kid’s term paper is always traumatic and the desire to pay the blackmail will always be high but it will mark you as a target and there is no guarantee that once you pay the money the attacker will remove the malware they might just make it go dormant for a while or do nothing leaving you twisting in the wind.
With how quickly this stuff is spreading and how easy it is to acquire eventually we’ll likely be up to our necks in it and we’ll see an appropriate government response. But even then we’ll need to make sure our stuff is safe. Stay up to date on this, put in place protections, and hopefully the next firm or person blackmailed won’t be you.