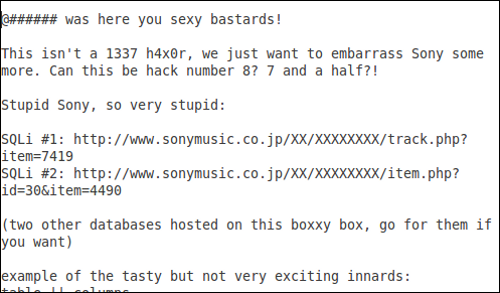
SonyMusic.co.jp is the latest casualty of an apparently decentralized hack and extract campaign against the hapless Japanese-based corporation.
Indeed, yet another SQL injection allowed digital infiltrators to deftly bypass Sony’s cyber perimeter and access restricted data on the above-mentioned website.
Fortunately, as Sophos Security researcher Chester Wisniewski points out, the database info that was published does not contain names, passwords or other personally identifiable information.
“[However], the attackers noted there are two other databases on the site that are vulnerable and it remains unclear whether they contain sensitive information,” Wisniewski explained.
“It [also] isn’t clear whether the hackers are able to inject data into the database, or simply access the tables and records it contains. If they are able to alter the records, this could be used to insert malicious code that could be used to compromise people browsing the site.”
According to Wisniewski, the attackers seem to be the “same crew” whic targeted Fox.com earlier this month.
“Known as Lulz Security, the group appears to attack sites primarily for fun and political reasons, not to steal credit cards and commit other types of fraud.
“[Of course], this doesn’t change the criminality of their behavior. Accessing systems without authorization is still a crime in most countries.”
Meanwhile, The Hacker News reports that Idahca – a Lebanese hacker group – managed to breach the database of ca.eshop.sonyericsson.com with just a simple SQL injection.
“Two attacks on Sony in one day. [This] morning LulzSec leaks Sony’s Japanese websites database and now Sony Ericsson’s Eshop database [has been] hacked.
“Email, passwords and names of 1000’s of users are exposed via text file on pastebin. They have [also] extracted the [entire] database and leak[ed] the [information] online via their Facebook/Twitter Accounts.”

So, is Sony capable of stopping the latest wave of SQL attacks against its infrastructure?
Well, Wisniewski believes the company has an “enormous target” on its back as a result of the ongoing and very public attacks.
“[Yet], it is unclear why this is happening [on a technical level]. Is Sony taking security seriously or are there simply so many flaws from the past that exist in their public facing sites that it will take them a long time to patch them all?
“[Yes], Sony has announced they are working with several professional organizations to get their security house in order and for their sake I hope this happens sooner rather than later.”






