Suits, ties and drones beware! A recent study has concluded that social media usage in corporate America is “fast outpacing” its system of rigid control.
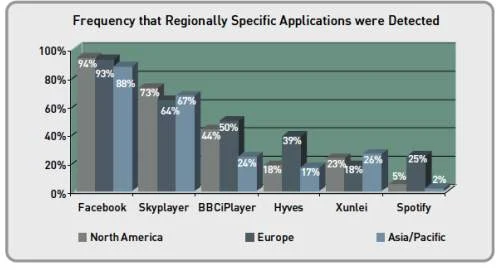
“Barriers to accessing applications are at an all-time low, accelerating the adoption of applications regardless of geography or vertical industry,” warned the Application Usage and Risk Report published by Palo Alto Networks.
“While financial services and healthcare workers increasingly rely on social media for business collaboration, they often ignore the associated risks such as non-compliance, data loss and threat propagation. These risks can jeopardize the company’s network as well as the integrity of the entire business operation.”
For example, a shocking 94 percent of the healthcare and financial services organizations included in the study used an average of 28 social networking applications, such as Facebook, Twitter and LinkedIn.
Both industries have regulations (such as HIPAA and FINRA) that require organizations to control and monitor information flow across social networking applications in order to protect the confidential data they manage.
However, because social networking apps use port 80 or port 443, all traffic is actually browser-based. This lack of visibility into social networking traffic could be a violation, or lead to violations, of compliance with industry rules and regulations.
“IT managers cannot simply block Enterprise 2.0 applications since they deliver clear business value. Nor can they simply allow these apps to run amok on their networks. IT needs to safely enable Enterprise 2.0,” explained Palo Alto Networks spokesperson René Bonvanie.
”By defining and enforcing policies that safely enable these apps, IT can enhance business productivity while mitigating security risks and compliance violations.”
Other key findings from the report include:
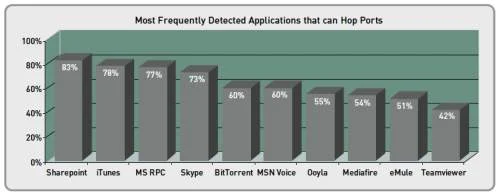
- Two-thirds of the 750 applications tracked, even client server and peer-to-peer (P2P) applications, can pass as Web traffic by hopping ports, using port 80, or hiding within SSL.
- This debunks the myth that ports 80 and 443 are reserved for browser-based traffic only. If P2P file sharing applications look like Web traffic, then they are difficult to detect and control – dramatically increasing the risk of inadvertent data leakage.
- Use of browser-based file sharing applications consumes 399 GB of bandwidth in financial services organizations, and 143 GB in healthcare firms.
- The one-to-one delivery nature of these applications minimizes the risk of inadvertent data loss or leakage, but does not prevent the purposeful movement of confidential data unless strict policy controls are in place.
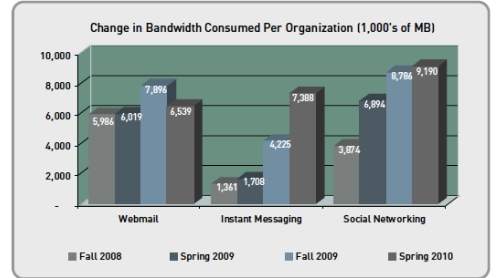
- The bandwidth consumed by social networking applications doubled in the last 18 months to 9GB per organization.